-
Wordpress vulnerabilities — where they come from and how they threaten the site
-
Vulnerability scanners: we use online services to check the site
-
How to protect a Wordpress site from hacking - step-by-step instructions
***
In the world of the Internet, you constantly have to choose between comfort and security. A simple password is more likely to be remembered - but it is easy to choose; installing programs downloaded from the Internet is convenient, but you can get an unpleasant "surprise" as a bonus that you did not expect.
Likewise, WordPress is an incredibly user-friendly content management system (CMS or engine) that makes life easier for webmasters. You no longer need to write the code yourself - it is enough to buy hosting and a domain for the site , install the CMS (now it can be done in a couple of clicks) and assemble the web resource using the designer. But... You don't know who released the "details", how responsibly they worked, and whether the attackers put some interesting features in there - besides the ones you need.
In the distant past, in the days of the first computers, everyone knew a guy who came, grumbled "they install everything in a row" and cleaned the endlessly slowed down device from viruses. In fact, we can all be that guy for our WordPress. Protecting Wordpress is not that difficult.
Read also: What is robots.txt and how to configure robots.txt for WordPress
What is Wordpress and why is it vulnerable
Wordpress is an open source content management system. It has a number of initial features by default, as well as three ready-made themes (site templates). But those who wish can release their own plugins (applications that perform certain functions on sites) and themes (templates).
These plugins and themes can be downloaded from the store and installed. Also, they simply exist on the Internet - for example, you can Google a query like worpdress templates and get a bunch of links. Thus, although the engine is written in PHP, it is not necessary to know it to create a simple page. The site on Wordpress will look professional and neat, even if it was not created by a designer or developer.
Wordpress plugins do everything — improve SEO, collect statistics, improve site structure, link payment tools, embed videos, social network icons, forums, tag clouds. In fact, all this can be done without even opening the site code editor or using it at a minimum. Many plugins and themes are free or shareware.
But each such plug-in is a code file that is installed on the site and gets access to it. No one can guarantee that among the useful code that improves the appearance and functionality of the site, there is not a piece of malicious code - the same virus - hidden.
Read also: Viruses on the website - how to find them and protect yourself from infection
Wordpress vulnerabilities — where they come from and how they threaten the site
When we download and launch a theme or plugin, we don't know what exactly we launched. Not everyone will climb into the code to check. And it can be written in such a way that attackers will be able to find a vulnerability and make their corrections, hack Wordpress and use the site for malicious purposes. For example, problems arise from improperly prescribed data cleansing — when something that shouldn't be there gets into a database containing sensitive information. Then attackers can make a so-called "injection" by embedding malicious code. There are quite a few weak spots that make it relatively easy to hack a Wordpress site.
Malicious code can:
-
contain viruses and other malicious software;
-
reset the administrator password and access information;
-
promote phishing — and this will directly lead to the loss of money and reputation, if it is an online store;
-
make automatic redirection to some sites, screw up views;
-
use the site's resources to organize DDoS attacks , embedding appropriate viruses in it, and much more.
For understanding, in just one week during April 2023, 70-80 vulnerabilities were discovered in themes and plugins that affected several million Wordpress sites.
Recently discovered Wordpress vulnerabilities
WordPress vulnerabilities are discovered regularly. Here's the news from thehackernews.com on May 6th - an innocent plugin for creating custom fields in Wordpress pages contained vulnerabilities that lead to reflected cross-site scripting. This is a type of attack that involves sending malicious code to users, causing their browser to perform unauthorized actions, such as allowing attackers to steal sensitive information. A reflection attack requires the user to follow a link that appears to be trustworthy. That is why they try to send it by e-mail or embed it in the pages of normal sites - in particular, with the help of vulnerabilities in Wordpress plugins.
But the popular Essential Addons plugin for Elementor contains the CVE-2023-32243 vulnerability, which allows an attacker to reset the password and take over the site.
The vulnerability of the engine itself was used by other attackers, who infect sites with their malicious code and redirect users to other, fraudulent pages in order to increase views of advertisements in Google Ads. Such views bring money, so the benefit is obvious. Itc.ua writes about it.
In short, Wordpress site security is an important issue, so let's move on to practical steps that will help save your site from trouble.
Read also: Where is the WordPress database stored
Vulnerability scanners: we use online services to check the site
Since a Wordpress site will have vulnerabilities by default, it would be strange not to learn how to identify them. For this, there are numerous services, both free and with additional functions for a certain fee. Vulnerabilities of WordPress are searched for:
-
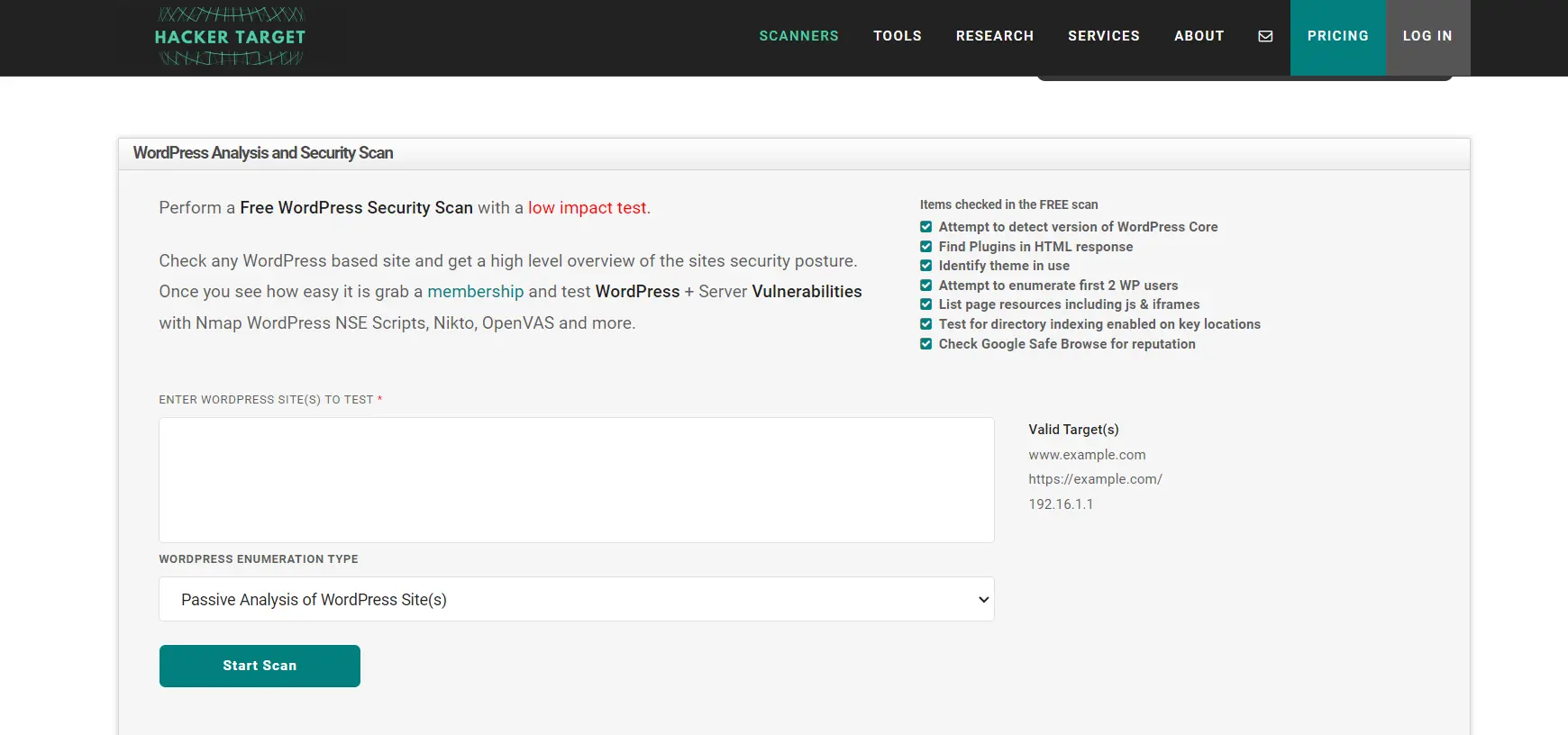
Hacker Target WordPress Security Scan tests the entire site, starting from the definition of the site's CMS , themes, plugins, the need for updates, problems with user records;
-
Scanurl will show the reputation of the site on the network: whether it will pass Google Safe Browsing, whether it has negative ratings, in particular in WebTrust, whether someone has marked it as dangerous, etc.;
-
Sucuri Website Malware and Security Scanner. We just talked about the company Sucuri in the context of finding vulnerabilities, and here is its product - it looks for all scripts on the site (will agree with those who understand scripts and will see the ones that have not been installed), firewall problems, the presence of the site in black lists, etc.;
-
UpGuard doesn't just scan, it outputs the results in a gamified form. It will look for malicious code, problems with antivirus protection, and much more.
Wordpress protection will be much more reliable if you use the chosen scanner at least once a month.
How to protect a Wordpress site from hacking - step-by-step instructions
As you can see, hacking Wordpress is quite possible. But this does not mean that it cannot be used. First, when vulnerabilities are discovered, developers of plugins and themes make so-called patches for them - code that closes the "weak spot". Second, the risks can be significantly reduced if safety measures are taken.
Site security on WordPress: admin protection
Most of the vulnerabilities that allow you to take control of the site are aimed at resetting the administrator's password and setting a new one. To avoid this:
-
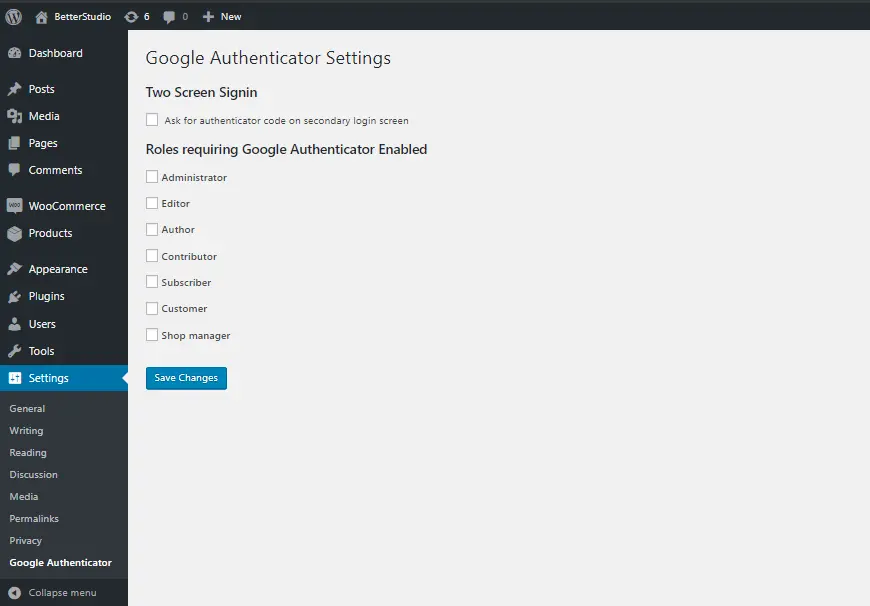
set up two-factor authentication. This function is offered by some security plugins — Jetpack, Wordfence. There are separate plugins specifically for this, including Google Authenticator. He suggests setting the second stage of login after entering the password — the answer to a secret question, an SMS code, etc.;
-
limit the number of password attempts. This can also be done with the help of plugins — in particular, Loginizer, Limit Login Attempts. You need to install one of these plugins and select the number of attempts in the settings;
-
create separate accounts for editors and content managers, limiting their rights to those necessary to work with content.
Read also: How to protect your Cityhost account in times of information instability
Choose proven WordPress themes and plugins
Wordpress plugins and themes are very easy to use. But it is important to choose those that are less likely to be affected.
Use proven plugins and themes. Wordpress itself suggests trusting the plugins and themes you download from its store. It is best to choose popular plugins and those that are updated frequently.
Don't forget to update your plugins and WordPress version
Responsible developers usually regularly test their products for WordPress vulnerabilities. When a vulnerability is found, it is fixed with a patch. To protect Wordpress:
-
regularly update plugins: if they had a vulnerability, it will most likely be fixed in the next versions;
-
regularly update the Wordpress system itself: new versions are also more secure.
Wordpress Security: Install custom security plugins
Each security plugin has its own set of features, they are different, and you have to choose how to protect Wordpress. After all, installing too many plugins is harmful to the speed of the site. Some plugins scan the site itself, others can deal only with certain consequences of a hack - for example, they will not allow you to reset your password, or they will make a backup of the site in time.

Here are some options you can use:
-
Sucuri in the free version allows you to test site files, it is also able to protect against DDoS attacks, scan for viruses, maintain a security certificate, etc.;
-
All in One WP Security & Firewall - includes a firewall, as the name suggests, but also offers many convenient functions to complicate site hacking - blocking the IP address if the password was entered incorrectly several times, notifications when some site files are changed, access to admin panel only during set working hours, logging of visits, captcha to complicate password selection, black list of files and much more;
-
Loginizer blocks the address of the user who entered the password incorrectly;
-
Jetpack was developed by Wordpress specifically to protect sites on this engine. It scans for viruses and worms, monitors traffic and all changes on the site, cuts off spam, etc. In addition, this plugin has functions for site optimization, collects statistics, offers convenient functions for electronic mailings and social networks;
-
Wordfence scans site files for integrity and security, monitors traffic and reports DDos attacks, and provides a firewall that stops hacking attempts, protects against hacker crawls, botnets, malicious traffic, and more. In addition, the plugin allows you to find malicious and phishing links on the site, if they appear.
There are a lot of security plugins, but it is worth looking for popular ones that are regularly updated and those that provide more functions at the same time.
Site protection: general tips
The security of the Wordpress site also depends on the implementation of general rules that reduce the likelihood of virus infection. It is worth administering it from a verified and protected computer, regularly scanning the computers of the entire team. It is also worth:
-
make backups on time;
-
set a good, complex password and change it regularly;
-
set unique logins for everyone who works with the site. You can even delete the admin account by first creating another account with administrator rights. This can be done through the "Users" menu item. The following option appears next to each existing user when hovering over it.
It is also important to install an SSL certificate on the site and switch to the https protocol. The fact is that by default, all data exchanges on the Internet are open (http protocol), and this allows attackers to wedge themselves between the server and the user's browser and steal sensitive information or redirect it. An SSL certificate is a kind of electronic passport that allows data exchange only after an encrypted connection is established. At the same time, it shows that following the link, the user goes exactly where he wanted - to this site. More expensive certificates also allow you to verify that a web page belongs to a specific company. It is especially important to have a security certificate if you:
-
collect personal data of users;
-
accept payments
Now more and more sites on the network are switching to encrypted protocols, so you should worry about your own.
There are probably as many ways to protect a WordPress site as there are ways to hack it. But they appear and improve gradually, so it is worth periodically updating the site and all available plugins, as well as at least sometimes paying attention to security news. It is not difficult, although it requires a little discipline and attention.