
We are experiencing not only a physical war, but also an information war. Now, when the news is about constant cyberattacks on Ukrainian services and their users, everyone must take care of the security of their account.
Cityhost specialists share tips on how to protect your account from hacking.
Check the correctness of contact data
Check the correctness of the contact data specified in your account (mail address, PIN, phone number). This data is easy to find in the account settings.
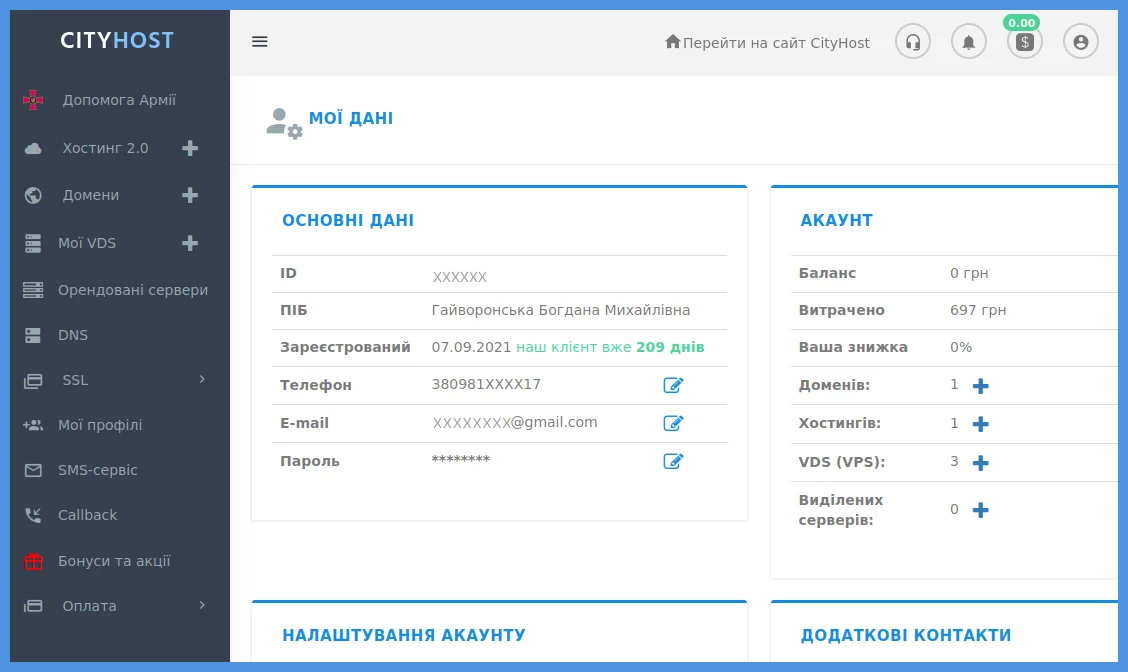
If an outsider gets into the control panel, they can easily change all passwords and use your site or important information on the server as they wish. To regain control, you must confirm your right to the services.
In case of loss of access, the system will first of all offer to restore it using a phone number or email. Therefore, the relevance of contacts is the first bastion of data protection. If you do not have access to them, this data can also be restored - write a statement to technical support. How to do it - read in the instructions .
And is it possible to change the last name or first name of the account owner if necessary? Yes, it is possible if there has been a change in life as well - marriage, divorce, change of name or surname in the passport for other reasons. You can see that there is no option to edit this data in the account, because such changes cannot be made at the first call of the heart, but only on legal grounds. You need to write an appropriate application and send it to technical support from your work account or registered mail, providing copies of documents that confirm the change of PIP.
If it is planned to transfer an account or a separate service to another person, it is done in a different way, using the procedure of transferring a hosting account or domain to a new owner.
We emphasize that when registering an account, you need to write only real, not fictitious data. If someone steals your account, technical support will only be able to help if you can prove ownership with proof of identity.
Set a complex password
Set a password that will be difficult to guess logically. We do not recommend using frequently used simple passwords, for example:
12345678
11111
qwerty
Date or year of your birth
Your name or surname
Do not use the same password for accounts on different sites. If attackers hack your mail or social network, they can also get into other accounts.
To prevent your password from being compromised, change it every six months.
Set up two-factor authentication using Google Authenticator
You have already met this way of protecting your account from hackers — it is widely used in Google, social networks, and payment systems. The procedure is that after entering the login and password, you need to go through an additional procedure that will prove that you are the one accessing the account, and not a fraudster who obtained the login and password by dishonest methods.
Activating the service is a matter of a few minutes. You need to find the "Two-step authentication" option in the settings, click on the "Management" button and follow the system prompts. At the same time, you need to install the application from the Play Market and link the Cityhost account to your mobile device using this application.
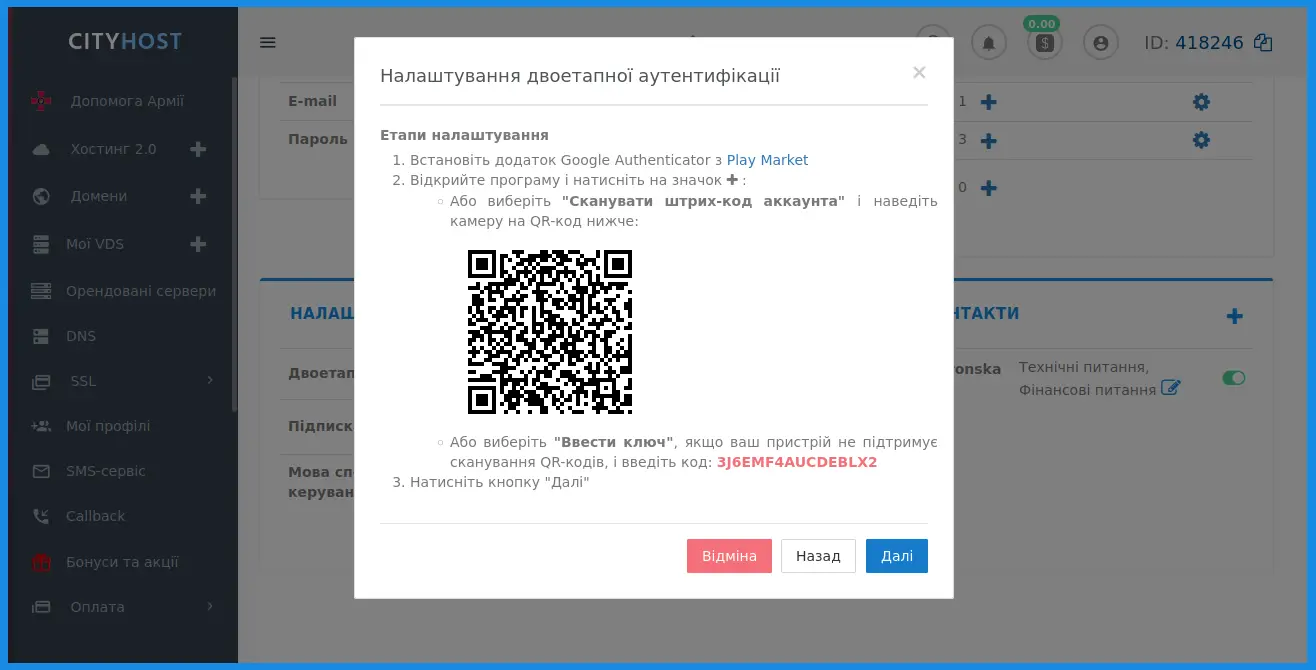
Once you have completed all the steps, the system will ask you to enter the code generated by your OTP application when logging into your account. To do this, you need to open the application on your smartphone and enter the code that will appear on the screen.
You can learn more about the connection algorithm from the instructions.
Update information in the "Delegation of services" section
In the control panel there is an option "Delegation of services". Thanks to it, you can delegate each service to an individual employee of your team, so that he can enter the account with his login and password and make settings only in the section for which he is responsible.
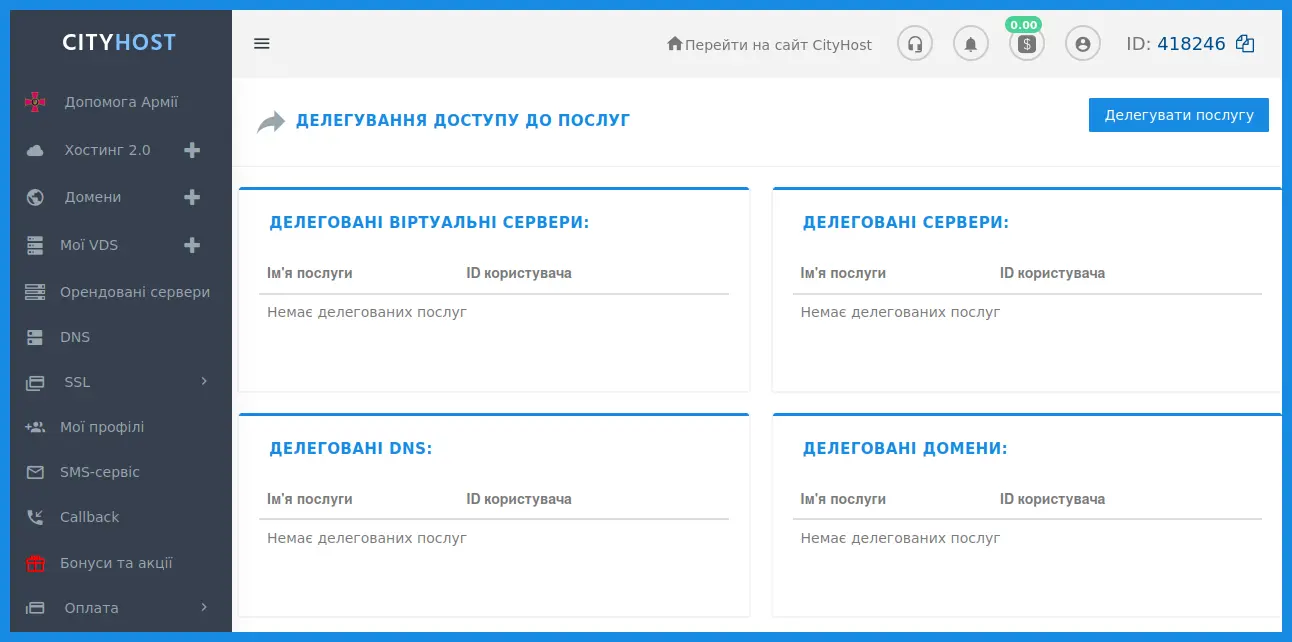
You can delegate the following services:
Hosting
Domain names
VDS servers
DS servers
DNS
If you have already used this option, go to the section and check the relevance of the data. Delete redundant delegated services if there is no longer a need to delegate their management - for example, an employee has resigned.
These steps are fairly easy and don't require much effort, but they can protect your account from theft or regain lost access. It's much easier than rebuilding sites from scratch or counting the damage from lost work information.





