One of the types of earnings for programmers is the search for vulnerabilities in the products of IT companies with the help of bug-bounty programs. This type of activity is called white hacking, and specialists are called ethical hackers or bug hunters. They look for defects in software and services and report them to company management, thereby helping to correct the error.
This is a goldmine for testers, who, compared to developers, have a slightly lower salary and can thus balance their financial capabilities. But in general, everyone who knows how to code can catch big fish — both amateurs and professional programmers.
Read also: " Learn to program on your own or go to developer courses - what to choose? »
What is a bug bounty
Bug-bounty is a policy of encouraging white hackers by companies. For reporting a vulnerability, you can get from a small fee of $100-150 to several hundreds of thousands of dollars. It all depends on how serious the error is, and what damages it could lead to if it were used by criminals.
What does the term bug bounty mean? Bug is a slang name for errors in the code, the word literally translates as "bug". Bounty means "reward", "gift".
Money is not always the reward — it can be, for example, free access to services. The motivation for finding bugs can also be gaining experience and learning. For example, Google offers the participants of its programs to donate the received reward to charitable organizations, if they did the work not for money.
Bug hunting is somewhat of a lottery. A hacker first finds a vulnerability, then creates a report about it (bug report), sends it to the company and waits for a solution. Depending on the importance of the error found and the level of its threat, the company independently determines the amount of the reward. Sometimes it can happen that the company will "take note" of the information provided, thank the hacker and that's the end of the cooperation. Therefore, before starting work, you must familiarize yourself with the rules of bug bounty programs, read which vulnerabilities are paid, and which are not considered important.
Also, everything depends on the quality of the report - if the bug hunter describes the problem in detail and offers methods to solve it, he will receive a higher reward than the one who provided a superficial report.
But even after doing a good job, a specialist cannot be sure that he will receive money. If several bug hunters report the same bug at once, the first one gets the prize.
Still, the rewards offered by the company are worth a try, as thanks to them you can get a fee from several hundred to several hundred thousand dollars, and the highest rate in bug bounty programs so far reaches two million.
Bug-bounty programs from companies
Reward programs can be divided into permanent and temporary:
Permanent programs are active all the time and are aimed at finding the most important and common errors in the code of products that are widely used by the consumer. By visiting the IT company's website, you will be able to find the rules for submitting reports and estimated payment amounts. Sometimes it happens that the company does not provide such a price, making separate decisions for each bug report. Entering the search query "company name + bug bounty" you will most likely find such a program.
Temporary programs are something like open testing, in which anyone can participate. The company announces the terms during which it accepts reports on discovered vulnerabilities and determines who will receive monetary rewards. New products are often tested this way.
Here we will talk about permanent programs from companies that you can use at any time.
Facebook, Instagram and other Meta products
Meta rewards white-collar hackers for finding vulnerabilities in its products, such as Facebook, Messenger, Instagram, WhatsApp, Workplace, and other applications, as well as open source applications. In the rules , you can read how you can perform error testing.
Testing can be carried out only from one's own account, or a test account, or someone else's, but only with written consent.
Sharing information about a discovered bug with someone is allowed only after the company conducts an investigation and makes a conclusion about the vulnerability.
When troubleshooting, you are not allowed to interact with other people's accounts or access their personal information without their written consent.
These are just some of the points that we decided to include in the article, in fact there are more of them. Each company has a similar list, so we emphasize once again - read the rules carefully before starting work.
Meta does not announce prices for found bugs, reserving the right to assign a reward on a case-by-case basis.
Amazon
One of the largest marketplaces in the world, Amazon, has published a list of rewards for bug hunters. The company emphasizes that the list indicates the highest possible rewards, and a more precise amount will be determined during the analysis of the bug report.
This is how the platform assesses found errors by risk:
Critical — $10,000-$20,000
High - $1500-$5000
Average — $350-500
Low threat level — $150
There are also a number of exclusions and caveats. Yes, the program's interests do not include bugs found in the IP space of AWS (this is a cloud technology platform that is owned by Amazon, but is still a different company).
It is forbidden to target test attacks on Amazon employees and customers and demand that you be paid for the found bug by threatening to use it against the company.
Microsoft
The brainchild of Bill Gates also announced a bug hunt and laid out a rather large list of rewards that can be obtained for bugs found.
The largest amounts are $100,000 each for vulnerabilities in Identity services, including Microsoft Account, Azure Active Directory, or selected OpenID standards, as well as for finding ways to bypass protections built into the latest version of the Windows operating system.
Apple
Apple has a fixed bounty program for certain types of vulnerabilities. You can read the price and the rules of receipt at the link .
One of the biggest rewards the company offers is for finding vulnerabilities through which a zero-click attack can be carried out.
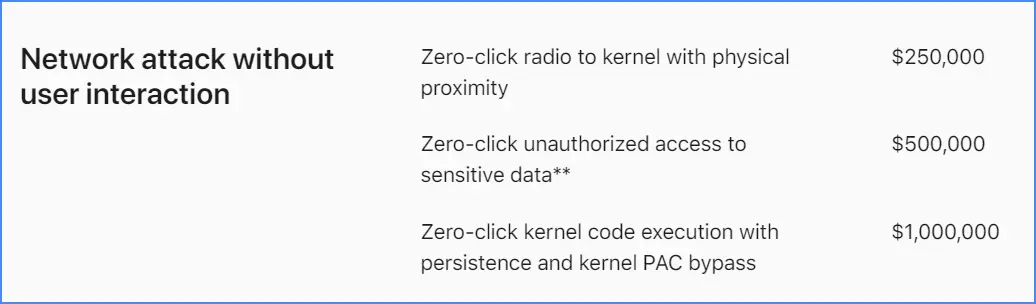
And this summer, Apple announced a security bug discovery fee for a new Lock Mode feature designed to protect users from spyware attacks. The bug bounty program will start working already this fall - stay tuned for the company's news.
Also, the IT giant has doubled the payment for effective searches for vulnerabilities in the blocking mode from the standard million to $2,000,000 — currently the highest sum for found bugs in the industry.
Google offers a bug bounty program for all of its products. This applies to all application services and services hosted on blogger.com , google.com, projectbaseline.com, youtube.com, verily.com, onduo.com, as well as Android OS, Chrome browser and third-party open source software, parts of which are used in the development of Google itself.
Now let's explain what the last phrase means. When creating software products, the company does not always rewrite the code, but can use open libraries. This allows you to save time and effort, and not to do unnecessary work that has already been done by other programmers. By paying compensation for such mistakes, the company not only protects itself and its customers, but also makes the entire Internet space safer.
The largest reward amount offered by the company is $31,337.
Read also: " How to remove Russian sites from Google search ".
PornHub
Well, porn sites also take care of their security, and personally such a well-known resource as PornHub. He jokes about the bug bounty program that it is a good way to combine the pleasant with the useful. Besides, by finding a bug on porn hosting, you can get up to $5,000.
By the way, you may have noticed that for Amazon and PornHub, the reward program is not located on the resource itself, but on a platform that specializes in intermediary services between bug hunters and IT companies. This is beneficial for projects that are too expensive to keep their own staff of experts who will render verdicts on bug reports.
Bug-bounty platforms
This is a separate type of business that allows young or local companies with small budgets, as well as services that do not do software development themselves, to use the services of white hackers. But the issue isn't just that not all companies have enough resources or staff to announce their own bug-finding program. Most projects are not so well known that bug hunters purposefully seek cooperation with them. That is why there are such "exchanges" on which IT companies present offers, and searchers try their hand at hunting for vulnerabilities.
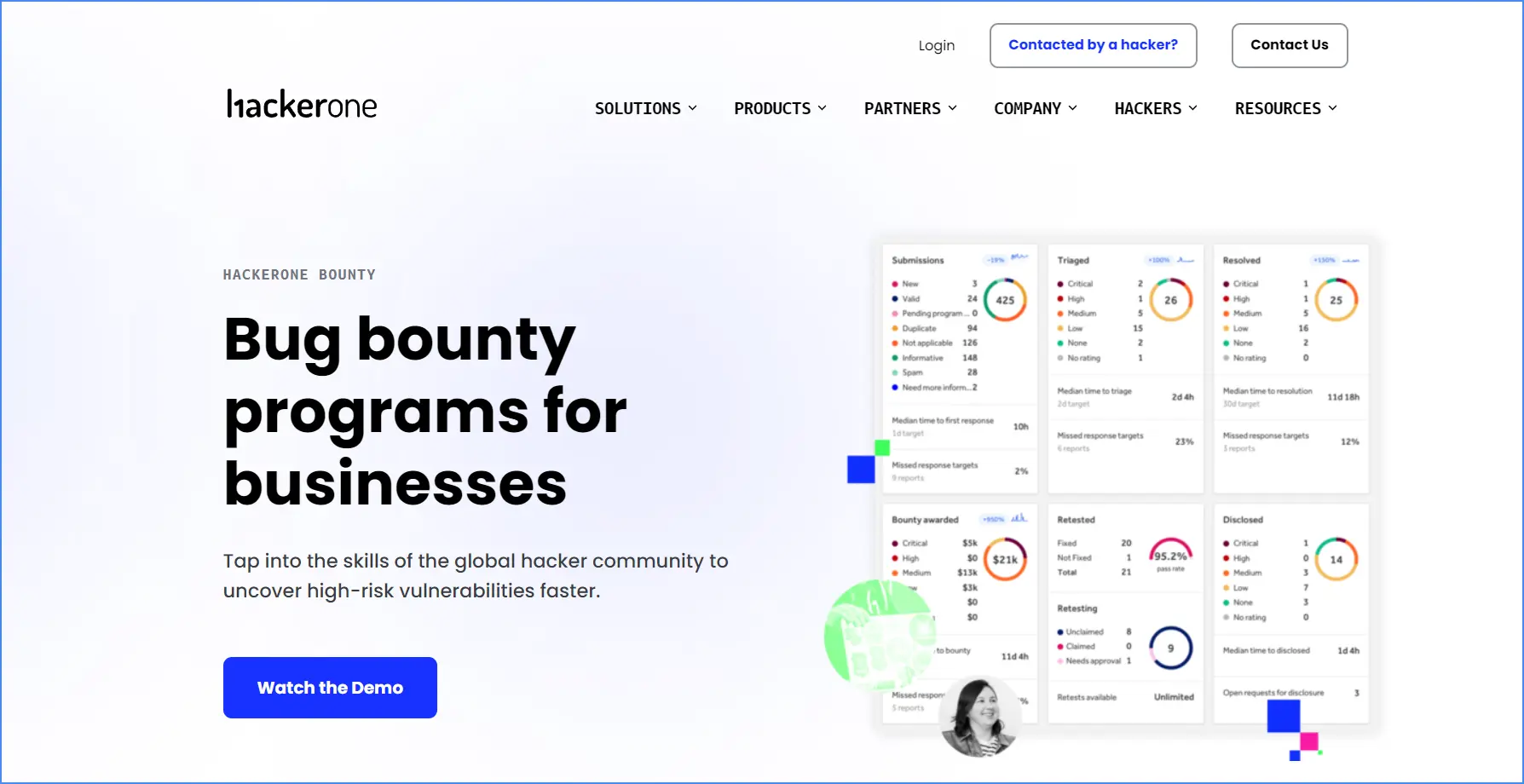
HackerOne
This is one of the oldest companies that began to use the experience of the white hacker community for the purpose of cyber security and offer their services to IT structures around the world. HackerOne has been around since 2012 and is headquartered in San Francisco, with offices in London and the Netherlands.
The company was created with the goal of making the Internet safer and has been declaring this idea as its main mission for 10 years.
Bugcrowd
A powerful crowdsourcing platform founded in 2011 in Australia. Bugcrowd specializes in a wide range of vulnerabilities and works with major global business players. Among them are such companies as Mastercard, Tesla, Fitbit, Atlassian, Square, Samsung; the platform even fulfills orders from the US Department of Defense and the Air Force. Works in almost 30 countries.
HackenProof
The Ukrainian bug bounty platform is part of the Hacken group of companies specializing in cyber security. HackenProof is one of the initiators of the search for vulnerabilities in Ukrainian state services in order to improve their security, and after the start of a full-scale invasion, it declared a cyber war on Russia.
The company was founded in 2017, but already cooperates with powerful players in the IT market and confidently competes with industry veterans.
***
This is a short excursion into the world of white hacking and rewards for finding bugs. There are many platforms and bug bounty programs, thanks to which you can make finding vulnerabilities your main specialty and make a good profit from it.
Read also: " Overview of foreign freelance exchanges: Upwork, Freelancer, Fiverr "